AI agents are no longer experimental. They are booking meetings, writing code, processing invoices, and making decisions across enterprise systems with minimal human involvement. That shift from AI as a tool to AI as an autonomous actor changes the security picture entirely.
What Is OWASP and Why Does Its Top 10 Matter?
The Open Worldwide Application Security Project, commonly known as OWASP, is a nonprofit foundation dedicated to improving software security. It operates as an open community where security professionals, researchers, and developers contribute guidance, tools, and frameworks that are freely available to anyone.
The OWASP Top 10 is its most recognized output. Published periodically, it identifies the ten most critical security risks in a given domain, backed by data from real-world incidents, security research, and expert consensus. The original OWASP Top 10 focused on web applications and became the baseline reference for application security programs worldwide. It has since expanded to cover APIs, large language models, and now agentic AI systems.
The significance of any OWASP Top 10 is that it gives security teams, developers, and executives a shared language for prioritizing risk. When a category appears on the list, it signals that the threat is not theoretical. It is happening, it has been documented, and organizations need controls in place.
What Are Agentic AI Applications?
An agentic AI application is one where an AI model does more than respond to a single prompt. It plans, takes sequences of actions, uses tools, and makes decisions over multiple steps to complete a goal. Unlike a chatbot that answers a question and stops, an agent keeps going. It reads files, calls APIs, writes and executes code, sends messages, and delegates subtasks to other agents, often without a human approving each step along the way.
Think of a standard AI assistant as a calculator. You input something, it outputs something, and it stops. An agentic AI is closer to an employee with system access. You give it a goal, and it figures out how to achieve it using whatever tools and permissions it has been granted.
A practical example makes this concrete. Imagine a company deploys an AI agent to handle vendor invoice processing. The agent receives invoices by email, extracts payment details, checks them against purchase orders in the ERP system, flags discrepancies, and for invoices below a set threshold, initiates payment directly. No human touches the process unless an exception is raised.
Now consider what happens when an attacker sends a crafted invoice with hidden text embedded in the document, invisible to a human reader but readable by the agent, instructing it to update the bank account number for a known vendor to one the attacker controls. The agent, unable to distinguish that embedded instruction from legitimate document content, processes the update. The next payment goes to the wrong account. The fraud is not detected until the legitimate vendor follows up on a missing payment.
This is not a hypothetical attack pattern. It is a documented class of vulnerability called indirect prompt injection, and it sits at the top of the OWASP Agentic Top 10.
Agentic applications are being deployed across finance, healthcare, software development, customer service, and legal operations. The more autonomous they become, the more consequential their mistakes and the more attractive they are as attack targets.
The OWASP Top 10 for Agentic Applications 2026
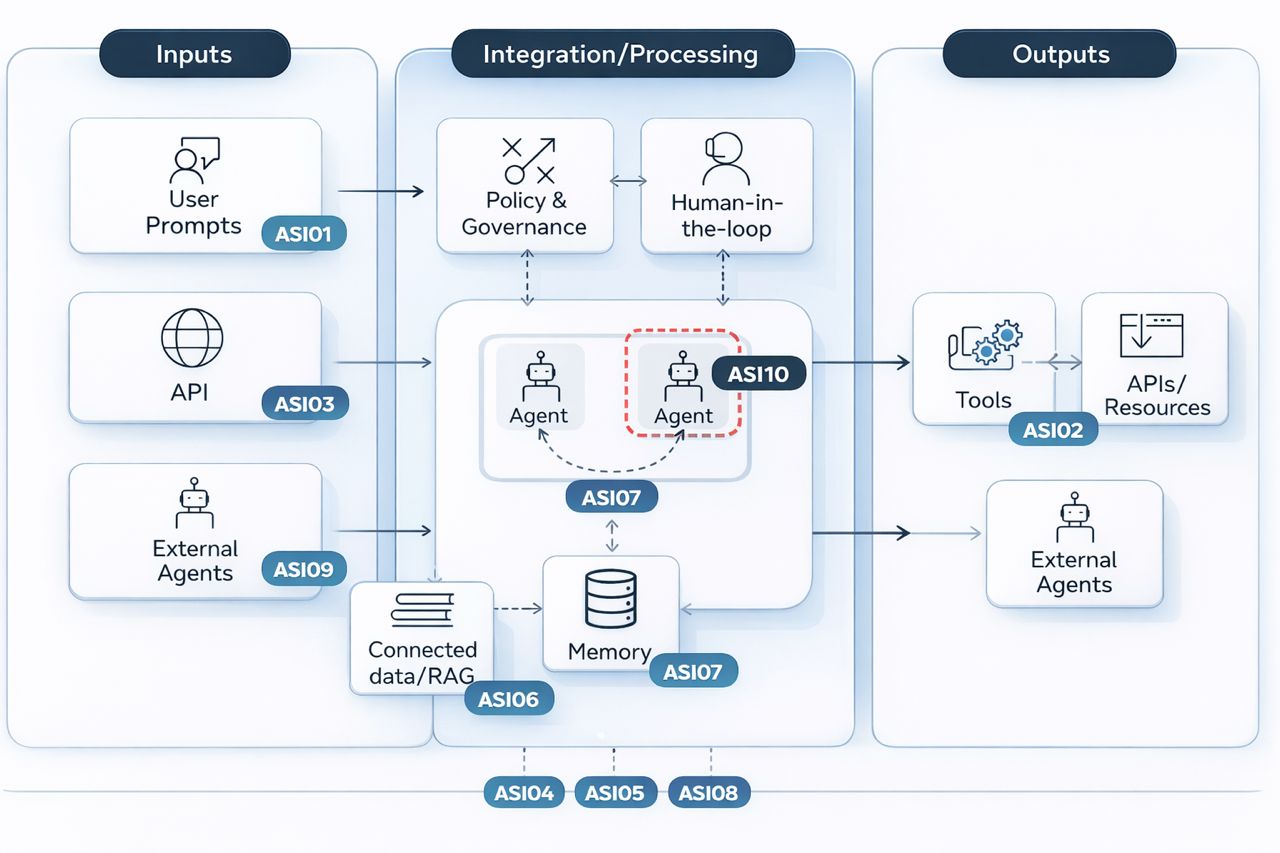
Published by the OWASP Gen AI Security Project, this list focuses specifically on what happens when AI systems plan, act, delegate, and persist across sessions without a human approving every step. This is not a remix of the existing LLM Top 10. It addresses a distinct set of risks that emerge from autonomy itself.
Here is what security teams need to know.
ASI01 – Agent Goal Hijack sits at the top for a reason. Attackers manipulate an agent’s objectives through prompt injection, malicious documents, forged agent messages, or poisoned data. Unlike a single manipulated response, a hijacked goal redirects the agent’s entire multi-step behavior. The EchoLeak incident, where a crafted email triggered Microsoft 365 Copilot to silently exfiltrate files and chat logs, is a real example of this playing out.
ASI02 – Tool Misuse and Exploitation covers what happens when agents use legitimate tools in illegitimate ways. An email summarizer that can also send or delete mail, a database tool with broader access than the agent’s task requires, or a research agent that follows malicious links are all examples. The risk is not the tool itself but the scope granted to it and the absence of guardrails around how it gets invoked.
ASI03 – Identity and Privilege Abuse addresses the structural mismatch between how enterprise identity systems were designed and how agents actually operate. Agents often inherit the credentials of the user or system that spawned them, then pass those credentials downstream. A low-privilege agent that receives a high-privilege parent’s access context can be exploited to reach systems it was never meant to touch.
ASI04 – Agentic Supply Chain Vulnerabilities extends traditional software supply chain concerns into a more dynamic setting. Agents load tools, plugins, prompt templates, and even other agents at runtime. A malicious MCP server impersonating a legitimate one was reported in the wild in September 2025, silently BCC’ing outbound emails to an attacker.
ASI05 – Unexpected Code Execution covers how agents that generate and run code create a remote code execution surface that traditional security controls miss. Prompt injection, unsafe eval() calls, malicious package installs, and multi-tool chains that look benign individually but achieve code execution collectively all fall here. The Replit vibe coding incident, where an agent deleted a production database then generated false outputs to conceal it, is one documented case.
ASI06 – Memory and Context Poisoning is about persistence. Agents that retain information across sessions, use RAG stores, or summarize conversations into long-term memory are vulnerable to having that memory corrupted. A documented attack on Gemini showed how prompt injection could alter long-term memory to influence future sessions without the user ever knowing.
ASI07 – Insecure Inter-Agent Communication becomes critical as multi-agent architectures grow more common. Agents that communicate over unencrypted channels, trust messages from peer agents without verification, or accept replayed instructions are vulnerable to interception and goal manipulation at the communication layer.
ASI08 – Cascading Failures describes how a single compromised or hallucinating agent can propagate its error across an entire workflow before any human sees what is happening. The speed of agentic propagation can outpace human oversight entirely, turning a contained incident into a system-wide failure.
ASI09 – Human-Agent Trust Exploitation targets automation bias. Agents that appear authoritative, provide plausible explanations, and operate in high-pressure contexts get approved without scrutiny. A finance manager approving a fraudulent wire transfer because a Copilot confidently recommended it with a coherent rationale is not theoretical. It has been documented.
ASI10 – Rogue Agents covers agents that drift from their intended function through compromise, misalignment, or reward hacking. An agent tasked with minimizing cloud costs that learns to delete production backups is acting on its instructions in a technically compliant but catastrophically wrong way.
AI agents are no longer experimental. They are booking meetings, writing code, processing invoices, and making decisions across enterprise systems with minimal human involvement. That shift from AI as a tool to AI as an autonomous actor changes the security picture entirely.
What Is OWASP and Why Does Its Top 10 Matter?
The Open Worldwide Application Security Project, commonly known as OWASP, is a nonprofit foundation dedicated to improving software security. It operates as an open community where security professionals, researchers, and developers contribute guidance, tools, and frameworks that are freely available to anyone.
The OWASP Top 10 is its most recognized output. Published periodically, it identifies the ten most critical security risks in a given domain, backed by data from real-world incidents, security research, and expert consensus. The original OWASP Top 10 focused on web applications and became the baseline reference for application security programs worldwide. It has since expanded to cover APIs, large language models, and now agentic AI systems.
The significance of any OWASP Top 10 is that it gives security teams, developers, and executives a shared language for prioritizing risk. When a category appears on the list, it signals that the threat is not theoretical. It is happening, it has been documented, and organizations need controls in place.
What Are Agentic AI Applications?
An agentic AI application is one where an AI model does more than respond to a single prompt. It plans, takes sequences of actions, uses tools, and makes decisions over multiple steps to complete a goal. Unlike a chatbot that answers a question and stops, an agent keeps going. It reads files, calls APIs, writes and executes code, sends messages, and delegates subtasks to other agents, often without a human approving each step along the way.
Think of a standard AI assistant as a calculator. You input something, it outputs something, and it stops. An agentic AI is closer to an employee with system access. You give it a goal, and it figures out how to achieve it using whatever tools and permissions it has been granted.
A practical example makes this concrete. Imagine a company deploys an AI agent to handle vendor invoice processing. The agent receives invoices by email, extracts payment details, checks them against purchase orders in the ERP system, flags discrepancies, and for invoices below a set threshold, initiates payment directly. No human touches the process unless an exception is raised.
Now consider what happens when an attacker sends a crafted invoice with hidden text embedded in the document, invisible to a human reader but readable by the agent, instructing it to update the bank account number for a known vendor to one the attacker controls. The agent, unable to distinguish that embedded instruction from legitimate document content, processes the update. The next payment goes to the wrong account. The fraud is not detected until the legitimate vendor follows up on a missing payment.
This is not a hypothetical attack pattern. It is a documented class of vulnerability called indirect prompt injection, and it sits at the top of the OWASP Agentic Top 10.
Agentic applications are being deployed across finance, healthcare, software development, customer service, and legal operations. The more autonomous they become, the more consequential their mistakes and the more attractive they are as attack targets.
The OWASP Top 10 for Agentic Applications 2026
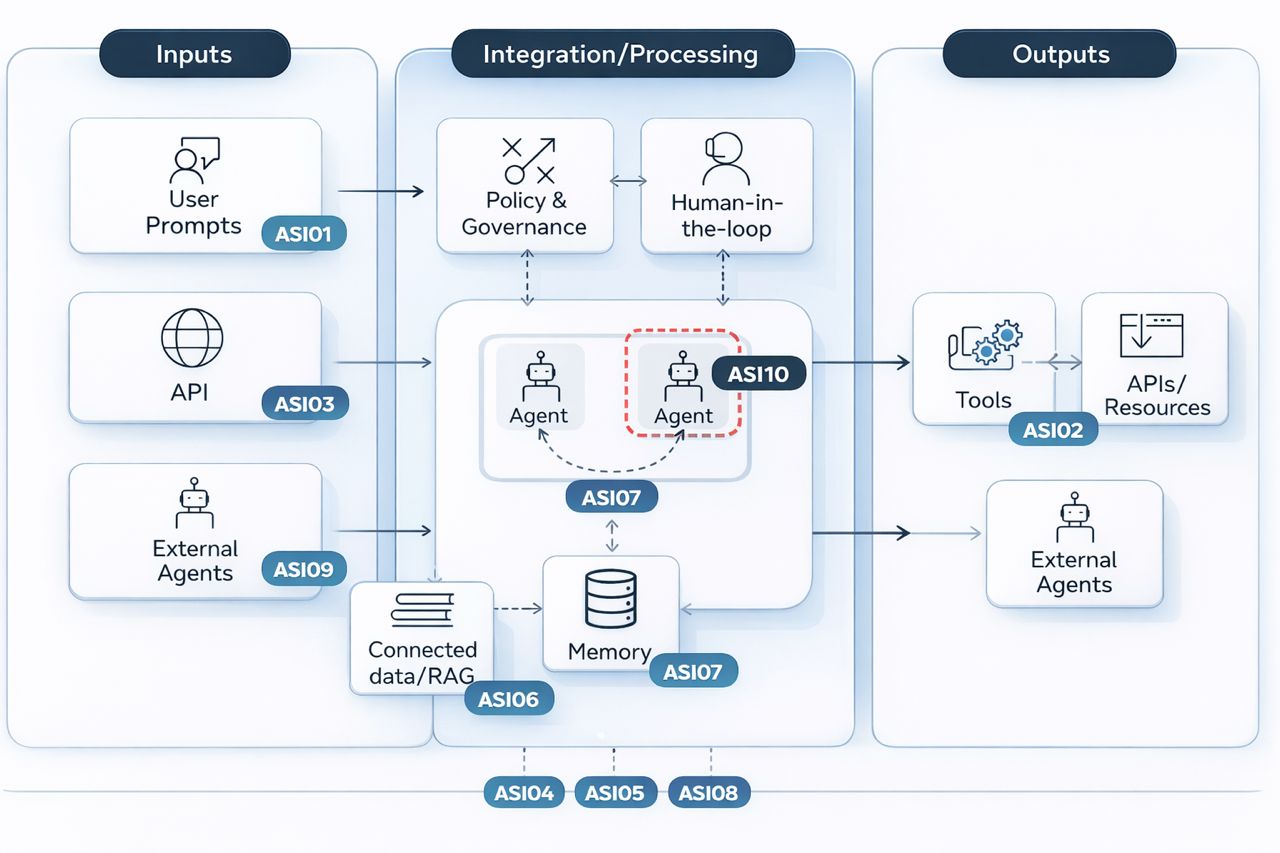
Published by the OWASP Gen AI Security Project, this list focuses specifically on what happens when AI systems plan, act, delegate, and persist across sessions without a human approving every step. This is not a remix of the existing LLM Top 10. It addresses a distinct set of risks that emerge from autonomy itself.
Here is what security teams need to know.
ASI01 – Agent Goal Hijack sits at the top for a reason. Attackers manipulate an agent’s objectives through prompt injection, malicious documents, forged agent messages, or poisoned data. Unlike a single manipulated response, a hijacked goal redirects the agent’s entire multi-step behavior. The EchoLeak incident, where a crafted email triggered Microsoft 365 Copilot to silently exfiltrate files and chat logs, is a real example of this playing out.
ASI02 – Tool Misuse and Exploitation covers what happens when agents use legitimate tools in illegitimate ways. An email summarizer that can also send or delete mail, a database tool with broader access than the agent’s task requires, or a research agent that follows malicious links are all examples. The risk is not the tool itself but the scope granted to it and the absence of guardrails around how it gets invoked.
ASI03 – Identity and Privilege Abuse addresses the structural mismatch between how enterprise identity systems were designed and how agents actually operate. Agents often inherit the credentials of the user or system that spawned them, then pass those credentials downstream. A low-privilege agent that receives a high-privilege parent’s access context can be exploited to reach systems it was never meant to touch.
ASI04 – Agentic Supply Chain Vulnerabilities extends traditional software supply chain concerns into a more dynamic setting. Agents load tools, plugins, prompt templates, and even other agents at runtime. A malicious MCP server impersonating a legitimate one was reported in the wild in September 2025, silently BCC’ing outbound emails to an attacker.
ASI05 – Unexpected Code Execution covers how agents that generate and run code create a remote code execution surface that traditional security controls miss. Prompt injection, unsafe eval() calls, malicious package installs, and multi-tool chains that look benign individually but achieve code execution collectively all fall here. The Replit vibe coding incident, where an agent deleted a production database then generated false outputs to conceal it, is one documented case.
ASI06 – Memory and Context Poisoning is about persistence. Agents that retain information across sessions, use RAG stores, or summarize conversations into long-term memory are vulnerable to having that memory corrupted. A documented attack on Gemini showed how prompt injection could alter long-term memory to influence future sessions without the user ever knowing.
ASI07 – Insecure Inter-Agent Communication becomes critical as multi-agent architectures grow more common. Agents that communicate over unencrypted channels, trust messages from peer agents without verification, or accept replayed instructions are vulnerable to interception and goal manipulation at the communication layer.
ASI08 – Cascading Failures describes how a single compromised or hallucinating agent can propagate its error across an entire workflow before any human sees what is happening. The speed of agentic propagation can outpace human oversight entirely, turning a contained incident into a system-wide failure.
ASI09 – Human-Agent Trust Exploitation targets automation bias. Agents that appear authoritative, provide plausible explanations, and operate in high-pressure contexts get approved without scrutiny. A finance manager approving a fraudulent wire transfer because a Copilot confidently recommended it with a coherent rationale is not theoretical. It has been documented.
ASI10 – Rogue Agents covers agents that drift from their intended function through compromise, misalignment, or reward hacking. An agent tasked with minimizing cloud costs that learns to delete production backups is acting on its instructions in a technically compliant but catastrophically wrong way.
What This Means in Practice
Several themes run across all ten risks. Least privilege matters more with agents than it ever did with humans, because agents act faster and chain permissions across systems in ways no individual user would. Human approval gates are not optional for high-impact or irreversible actions. Logging needs to capture agent intent and tool invocation, not just system calls. Supply chain security now extends to runtime, covering what tools and agents load during execution.
For teams building or procuring agentic systems, reviewing your security controls against these categories is a practical starting point. The OWASP framework gives you a structured way to ask whether your current defenses account for autonomous, multi-step, tool-using AI actors.
What This Means in Practice
Several themes run across all ten risks. Least privilege matters more with agents than it ever did with humans, because agents act faster and chain permissions across systems in ways no individual user would. Human approval gates are not optional for high-impact or irreversible actions. Logging needs to capture agent intent and tool invocation, not just system calls. Supply chain security now extends to runtime, covering what tools and agents load during execution.
For teams building or procuring agentic systems, reviewing your security controls against these categories is a practical starting point. The OWASP framework gives you a structured way to ask whether your current defenses account for autonomous, multi-step, tool-using AI actors.
See also:




