- About Us
-
-
- About UsWe are the regional leaders in cybersecurity. We are masters in our tradecraft. We are dynamic, talented, customer-centric, laser-focused and our mission is to defend and protect our customers from cyber adversaries through advisory, consulting, engineering, and operational services.
-
-
- Solutions
-
-
- SolutionsThe cybersecurity industry is fragmented. We have carefully curated an interoperable suite of cybersecurity products and solutions that focus on improving your security compliance and risk maturity that add real business value, effectiveness, and ROI. Combined with our professional services and security engineering expertise we design, architect, implement and operate complex environments and protect your digital space.
-
- Industry
-
-
- IndustryCyber adversaries and threat actors have no boundaries. No industry is immune to cyber-attacks. Each industry has unique attributes and requirements. At DTS we have served all industry verticals since inception and have built specialization in each segment; to ensure our customers can operate with a high degree of confidence and assurance giving them a competitive advantage.
-
- Services
-
-
- ServicesOur cybersecurity services are unmatched in the region. With our unique customer-centric approach and methodology of SSORR we provide end-to-end strategic and tactical services in cybersecurity. We on-ramp, develop, nurture, build, enhance, operationalize, inject confidence, and empower our customers.
-
-
- Vendors
- Products
- Resources
- Press Center
- Tweets
- Support
- Contact
-
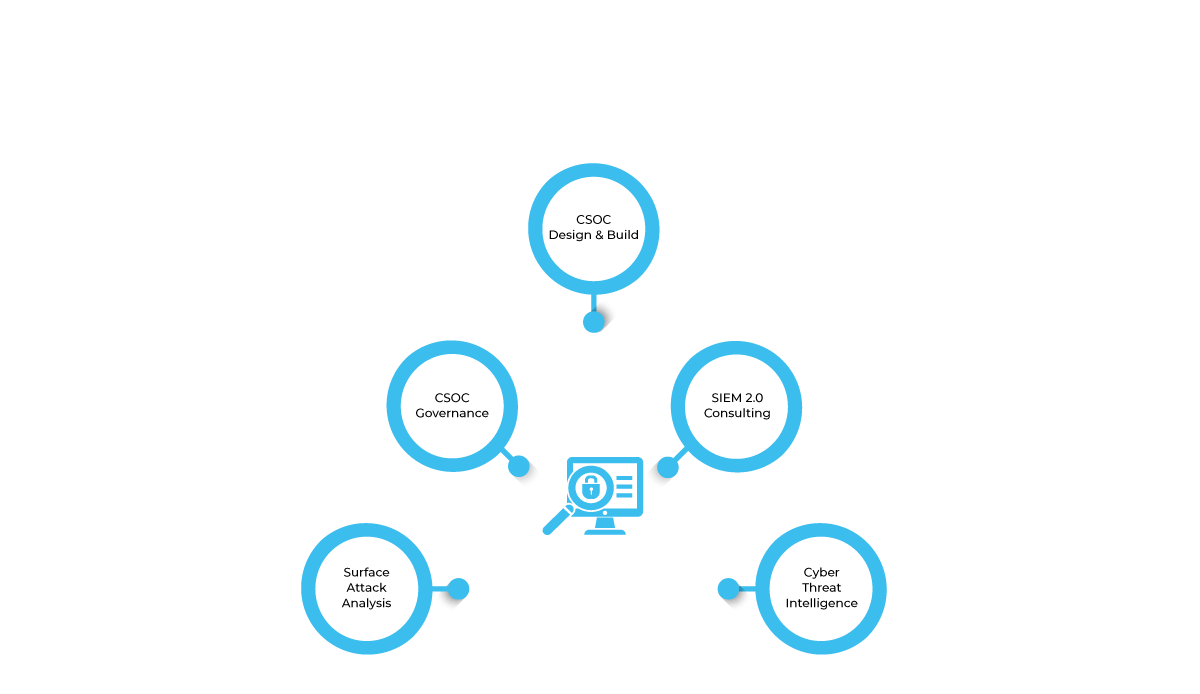
Cyber Operations
DTS Solution has been involved in designing and developing Cyber Security Operations Center (CSOC) for many tier 1 organizations in the region. The development of CSOC to ensure cyber risks and attacks are monitored on an on-going basis and not just during an incident. CSOC development consisting of people, process, technology and business contexts are all identified prior to the build phase. DTS Solution has also contributed to the SOC CMM (Capability Maturity Model) assessment – an open source framework to assess the current level of CSOC maturity based on the various different domains.
Cyber Security Operations
Cyber Security Operations
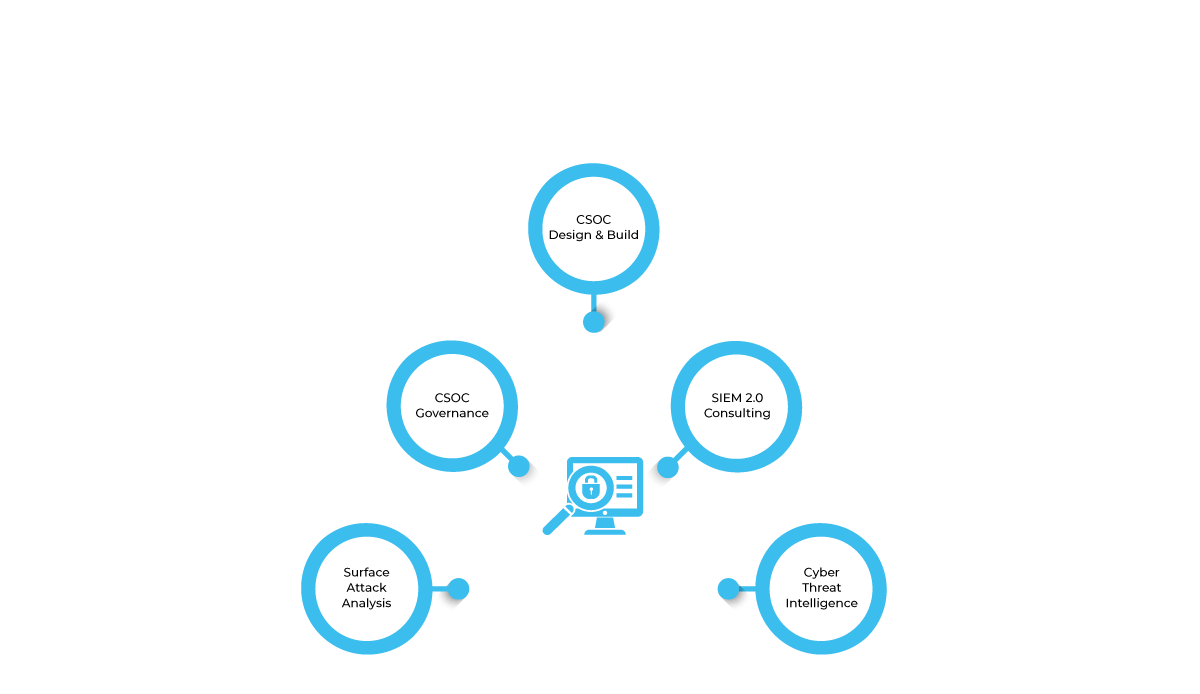
CSOC Design and Build
- CSOC Strategy
- CSOC Design and Build
- CSOC Operating Model (In-House, Managed or Hybrid)
- CSOC Physical Layout and Conceptual Design
CSOC Governance
- CSOC Policies
- CSOC Processes
- CSOC Procedures (SOPs)
- Performance – SLAs, KPIs and Metrics
- CSOC Organizational Structure and Competency Center
CSOC Technology
- SIEM 2.0 Consulting
- Security Platform Eco-System
- Vulnerability and Patch Management
- Configuration Management
- Advanced Malware Analysis
- Policy Compliance
- Threat Hunting
- Server and Endpoint Forensics
- Threat Intelligence Platform
- Security Orchestration and Automation Response (SOAR)
- Asset Management
- Network and Security Infrastructure Components
- Identity and Access Management
- Privileged Account Monitoring
- Application Security – Web and Database
- Data Leakage Prevention
- Remote Access
- Email Security
Surface Attack Analysis and Threat Modeling
- Threat Modeling Methodology
- Network Architecture Review
- Cyber Attack Kill Chain
- MITRE ATT&CK Matrix
- Threat Detection Use Cases
- Use Case Development and Implementation
- Incident Response Playbook
Cyber Threat Intelligence
CSOC Design and Build
- CSOC Strategy
- CSOC Design and Build
- CSOC Operating Model (In-House, Managed or Hybrid)
- CSOC Physical Layout and Conceptual Design
CSOC Governance
- CSOC Policies
- CSOC Processes
- CSOC Procedures (SOPs)
- Performance – SLAs, KPIs and Metrics
- CSOC Organizational Structure and Competency Center
CSOC Technology
- SIEM 2.0 Consulting
- Security Platform Eco-System
- Vulnerability and Patch Management
- Configuration Management
- Advanced Malware Analysis
- Policy Compliance
- Threat Hunting
- Server and Endpoint Forensics
- Threat Intelligence Platform
- Security Orchestration and Automation Response (SOAR)
- Asset Management
- Network and Security Infrastructure Components
- Identity and Access Management
- Privileged Account Monitoring
- Application Security – Web and Database
- Data Leakage Prevention
- Remote Access
- Email Security
Surface Attack Analysis and Threat Modeling
- Threat Modeling Methodology
- Network Architecture Review
- Cyber Attack Kill Chain
- MITRE ATT&CK Matrix
- Threat Detection Use Cases
- Use Case Development and Implementation
- Incident Response Playbook
Cyber Threat Intelligence
Threat intelligence information can vary from Indicator of Compromise (IOC), Command and Control (C&C), Open Source Intelligence – Artefact Leakage, Email Accounts, Dark Web Crawling, Compromised Accounts, Digital Risks and Footprint. In some cases, we also offer brand reputation protection and take down services.
Solutions
Network and Infrastructure Security
Zero Trust and Private Access
Endpoint and Server Protection
Vulnerability and Patch Management
Data Protection
Application Security
Secure Software and DevSecOps
Cloud Security
Identity Access Governance
Governance, Risk and Compliance
Security Intelligence Operations
Incident Response
Accreditations






Accreditations






Dubai
Office 7, Floor 14
Makeen Tower, Al Mawkib St.
Al Zahiya Area
Abu Dhabi, UAE
Sama Tower, Floor 7
Moh. Thunayan AlGhanim Str.
Jibla, Kuwait City
Kuwait
160 Kemp House, City Road
London, EC1V 2NX
United Kingdom
Company Number: 10276574
Riyadh
Office 109, Aban Center
King Abdulaziz Road
Al Ghadir
Riyadh, Saudi Arabia
The website is our proprietary property and all source code, databases, functionality, software, website designs, audio, video, text, photographs, icons and graphics on the website (collectively, the “Content”) are owned or controlled by us or licensed to us, and are protected by copyright laws and various other intellectual property rights. The content and graphics may not be copied, in part or full, without the express permission of DTS Solution LLC (owner) who reserves all rights.
DTS Solution, DTS-Solution.com, the DTS Solution logo, HAWKEYE, FYNSEC, FRONTAL, HAWKEYE CSOC WIKI and Firewall Policy Builder are registered trademarks of DTS Solution, LLC.
Resources
To check the resource item, enter your name and email address
