The event recognized the efforts of several cybersecurity initiatives at the individual, corporate and government level
- Understand the Organization and Line of Business
- Physical and Logical Security Architecture Review
- Define Assets
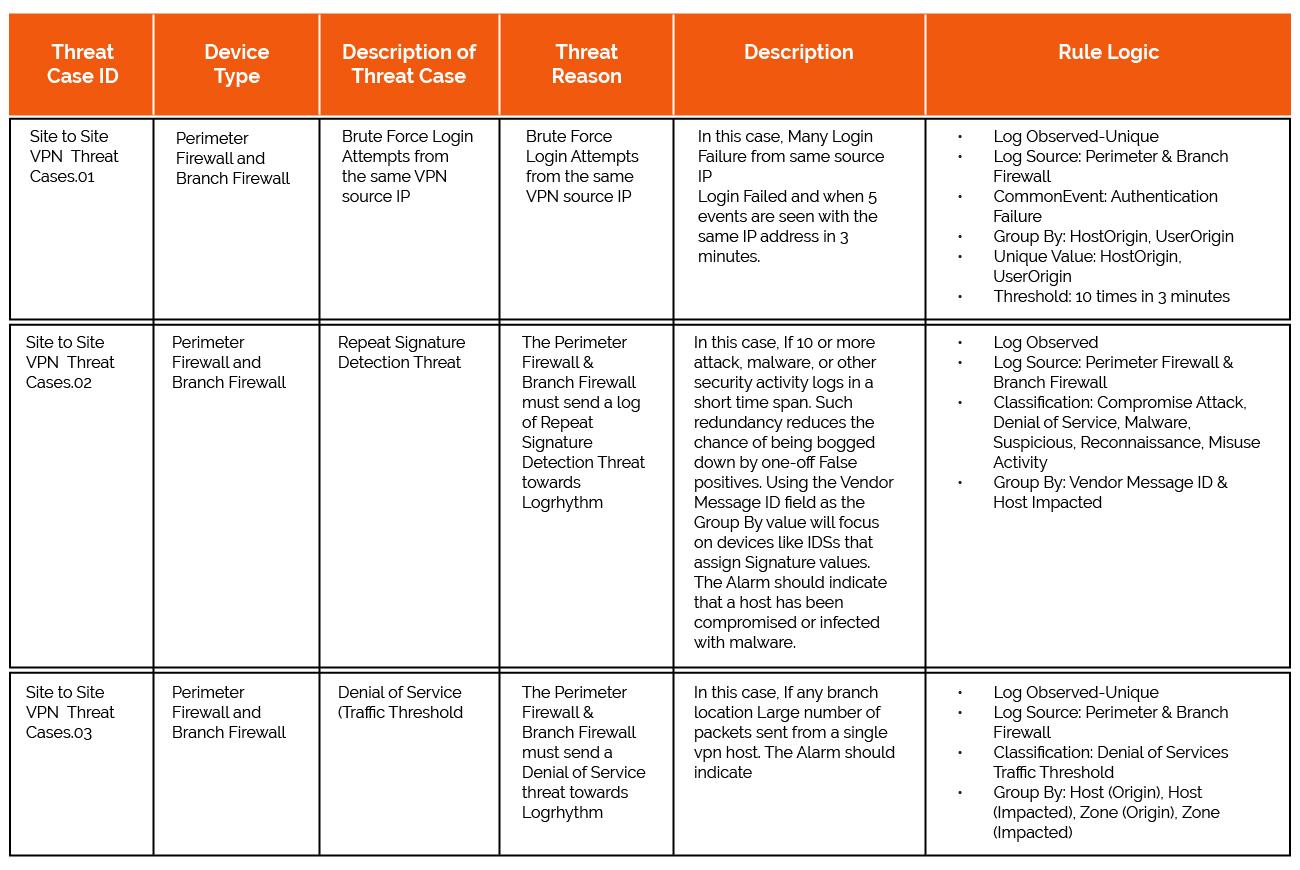
- Identify the Vulnerabilities, Threats, and Risks
- Review the Countermeasures and Gap Analysis
- Integrate your Security state to SOC
- Monitor-Tune-Mature
The event recognized the efforts of several cybersecurity initiatives at the individual, corporate and government level
Organizations spend most of their money and resources on security, sometimes more than actual operations. Because they understand that the unauthorized revealing of a single bit of code could possibly put an end to their business. However, none is immune to cyber-attacks. Security professionals within the organization would equip their defense with all the tools they can accommodate assuming to deter any attacker. This is like a wild fire. Along with the new tools they bring new vulnerabilities to the Network infrastructure. Above all, attackers are so patient to wait for the right chance to get access to your data as they know it values a lot. Even the smallest negligence in security infrastructure could be an invitation to the attacker.
- Understand the Organization and Line of Business
- Physical and Logical Security Architecture Review
- Define Assets
- Identify the Vulnerabilities, Threats, and Risks
- Review the Countermeasures and Gap Analysis
- Integrate your Security state to SOC
- Monitor-Tune-Mature
See also: