Modern day cyber threats are ever increasing in sophistication and evasiveness against Process Control Networks. Organizations in the industry are facing a constant challenge to adopt modern techniques to proactively monitor the security posture within the SCADA infrastructure whilst keeping cyber attackers and threat actors at bay. In this presentation the fundamental building blocks of building a SCADA cyber security operations center with key responsibilities such as Incident Response Management, Vulnerability and Patch Management, Secure-by-design Architecture, Security Logging and Monitoring and how such security domains drive accountability and act as a line of authority across the PCN was covered.
Modern day cyber threats are ever increasing in sophistication and evasiveness against Process Control Networks. Organizations in the industry are facing a constant challenge to adopt modern techniques to proactively monitor the security posture within the SCADA infrastructure whilst keeping cyber attackers and threat actors at bay. In this presentation the fundamental building blocks of building a SCADA cyber security operations center with key responsibilities such as Incident Response Management, Vulnerability and Patch Management, Secure-by-design Architecture, Security Logging and Monitoring and how such security domains drive accountability and act as a line of authority across the PCN was covered.
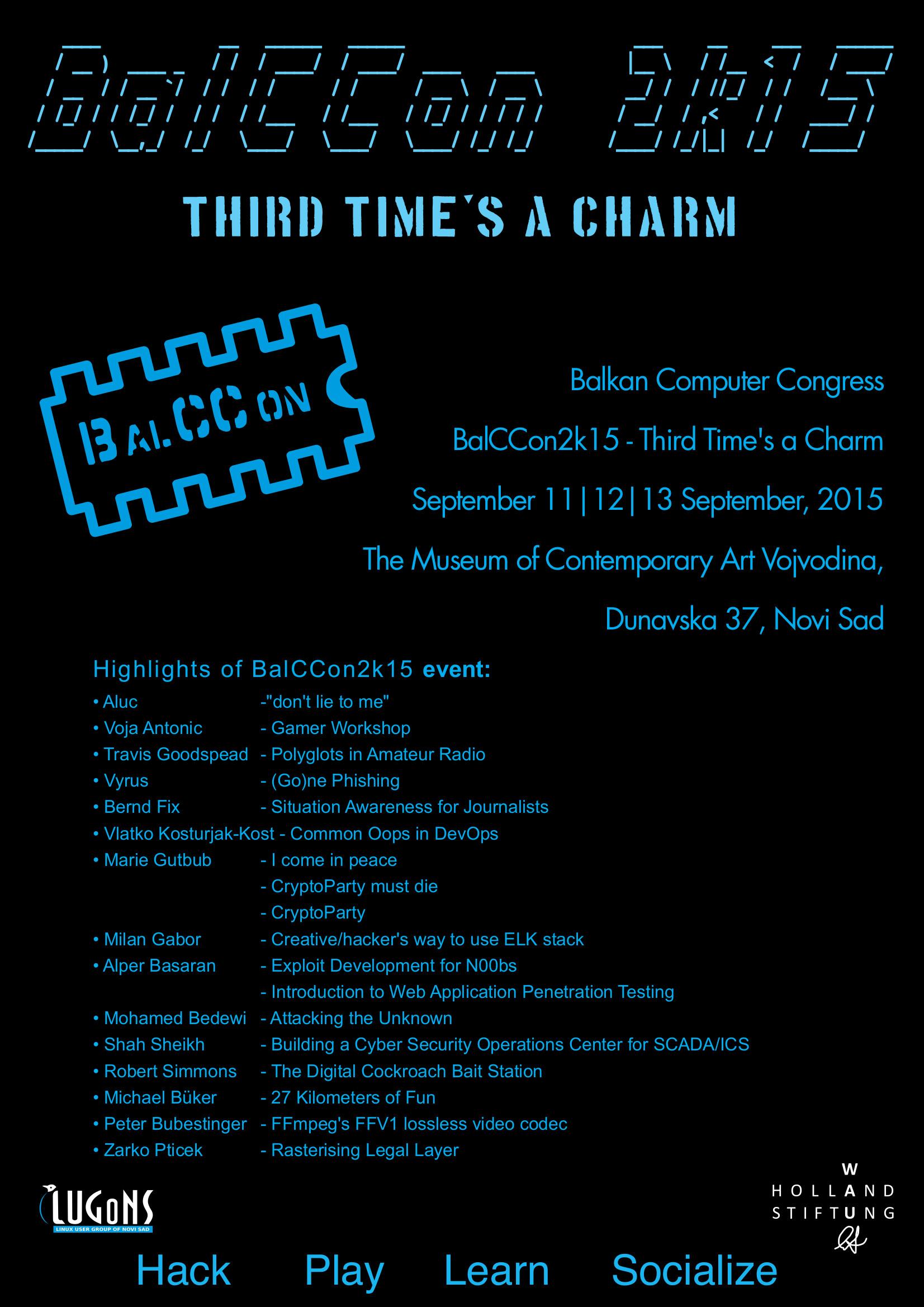
Mohamed Bedewi - Attacking the Unknown

Mohamed Bedewi - Attacking the Unknown