Quantum computing is advancing fast enough to challenge the encryption that secures critical systems across the UAE. The nation has taken a decisive step ahead of that risk with Executive Regulation No. 71 of 2024, issued by the UAE Cybersecurity Council. This regulation mandates a structured cryptographic migration program for government and vital sector entities, shifting away from vulnerable classical algorithms toward quantum-resistant controls.
A Post-Quantum Cryptography Readiness Assessment allows organizations to measure their exposure, identify weak cryptographic assets, and prepare for the UAE’s transition cycle without disrupting essential services. The assessment becomes the foundation for long-term confidentiality, system integrity, and compliance with national cryptographic requirements.
Quantum computing is now a pressing issue for national security and the economy, not just a future concern. The UAE has demonstrated proactive leadership worldwide by approving the National Encryption Policy and issuing its mandatory Executive Regulation to protect the
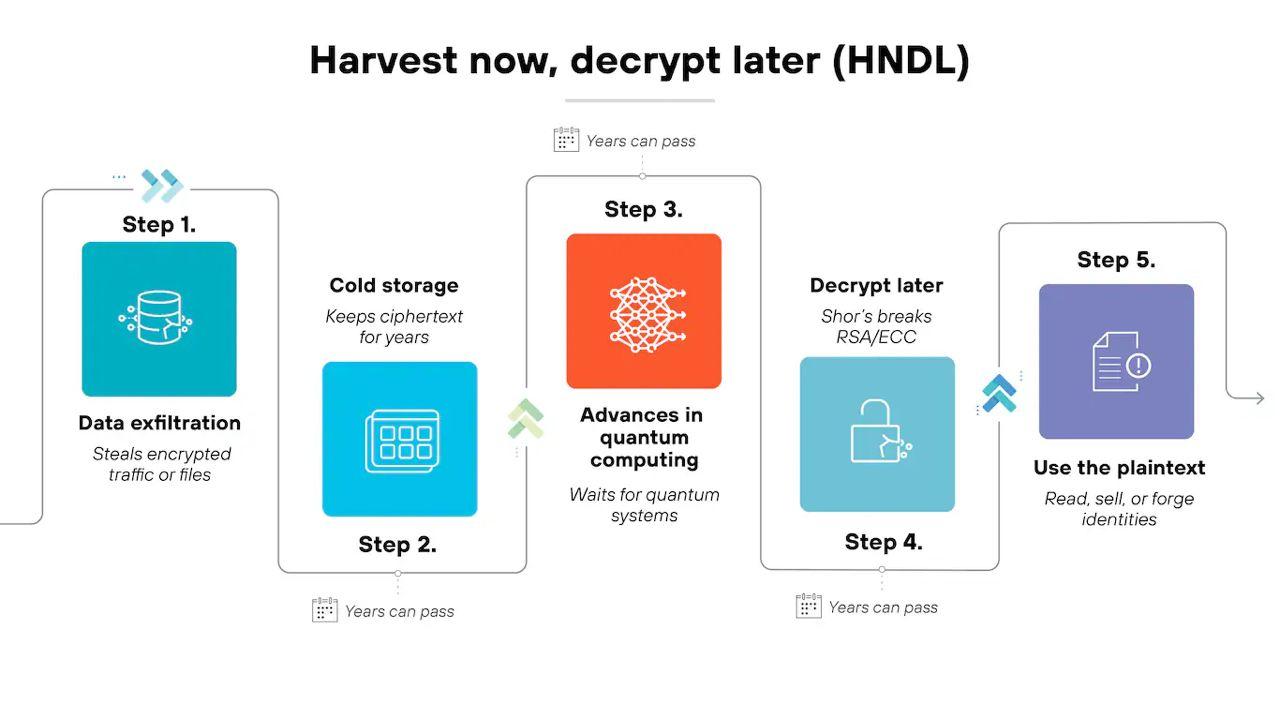
The Harvest Now, Decrypt Later Problem
Understanding Cryptographic Assets
Cryptographic assets are tools or services that provide cryptographic security for data and communications critical to organizational operations. These include software such as code, libraries, applications, and implementations of cryptographic algorithms or protocols. They also encompass data like certificates and cryptographic keys, as well as hardware tokens, HSMs (Hardware Security Modules), smart cards, trusted execution environments (TEEs), and physical pseudorandom generators.
The regulation classifies cryptographic assets into two critical categories:
Category A – Highly Sensitive Assets:
- Encryption Devices and Virtual Private Networks (VPNs)
- Radio Communication Solutions
- Key Management Systems
- Secure Communication Solutions (Email Security Systems, Secure Messaging Application Systems, Audio/Video Applications, Web Conferencing)
Category B – Support Infrastructure:
- Cloud Encryption Solutions
- File and Data Sharing Solutions
- Network Devices (Firewalls, Routers)
- Smart Card Readers
- PLC and SCADA Systems
All these assets are subject to mandatory migration and compliance verification under the regulatory framework.
Why Organizations Need a Structured PQC Readiness Assessment
Quantum impact is uneven across industries. Financial services, telecom operators, governments, energy providers, healthcare institutions, and global enterprises hold data that must remain confidential for decades. A breach today carries a long tail because attackers can store encrypted material until it becomes solvable.
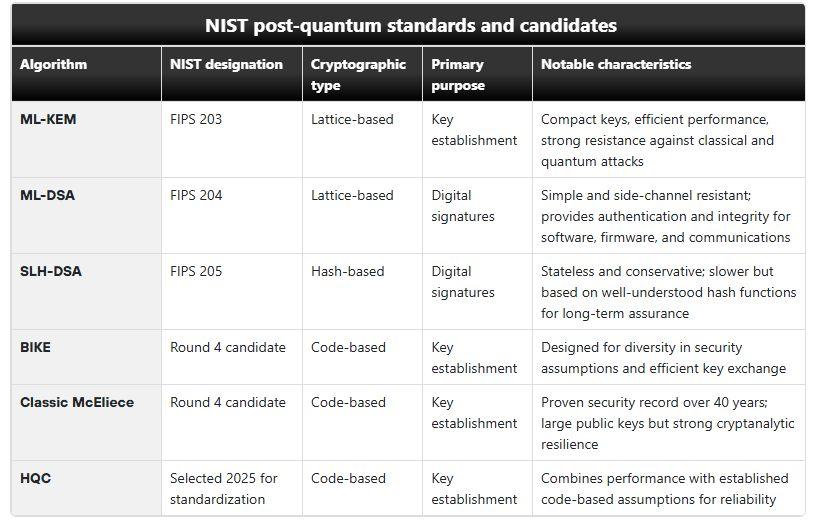
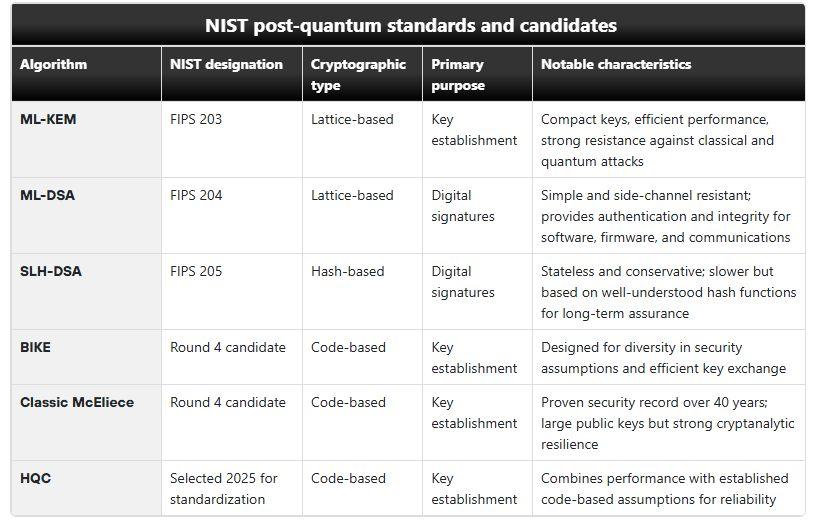
NIST has already standardized its first set of quantum-resistant algorithms. Major vendors are shipping hybrid modes that combine classical and PQC primitives. International bodies such as ETSI, IETF, and ISO are defining transition rules. The regulatory shift has already begun.
A readiness assessment gives teams the groundwork required to move without causing operational disruption. It answers three core questions:
Which systems depend on cryptography today?
Which components break the moment PQC becomes a requirement?
What must be replaced, upgraded, or redesigned to maintain confidentiality and authenticity?
The organizations that move early reduce both the migration effort and the cost of downtime. Many crypto assets live much longer than expected, and replacing them under pressure is significantly harder. Long-lived certificates, archived backups, and stored sensitive records all fall into this category.
Minimum Cryptographic Requirements
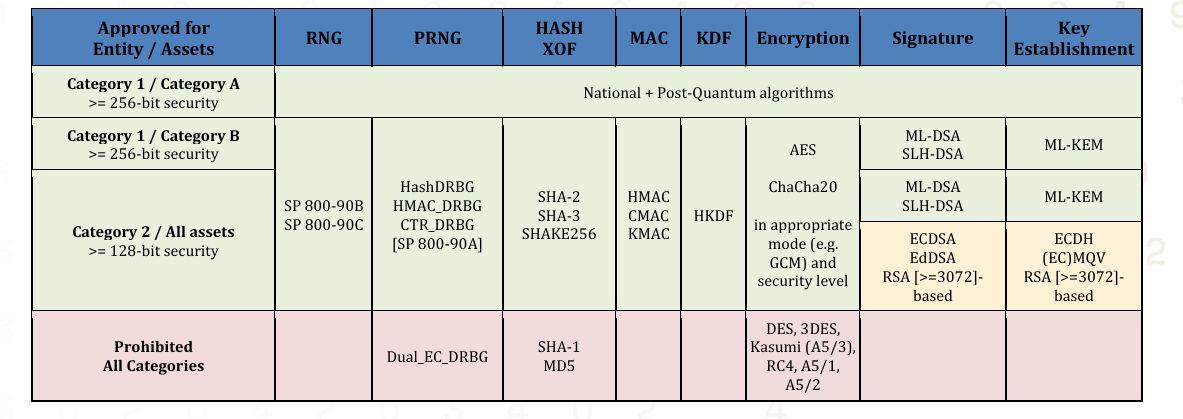
The regulation establishes specific minimum cryptographic requirements for each entity category.
Category 1 Entities Must:
- Achieve cryptographic agility
- Use at least 256-bit security/PQC Category 5 security strength
- Use approved Category A assets (VPN, ESS, SMAS)
- Employ national cryptography for Category A assets minimum
- Implement post-quantum cryptography
- Use approved hardware-protected cryptography when applicable
- Utilize cryptographic certificates from approved certificate authorities
Category 2 Entities Must:
- Use at least 128-bit security strength
- Employ standard cryptography
Category 2 entities are recommended to use post-quantum cryptography with security strength meeting established standards.
The regulation explicitly prohibits certain algorithms. Unless explicitly authorized, any algorithms not mentioned in the regulations are considered unapproved and cannot be used. Banned algorithms include Dual_EC_DRBG, SHA-1, MD5, DES, 3DES, Kasumi (A5/3), RC4, A5/1, and A5/2.
Technical Migration Realities
Post-quantum algorithms require larger keys than current standards. ML-KEM public keys need 1,184 bytes versus 256 bytes for RSA-2048. ML-DSA signatures use around 3,309 bytes compared to 256 bytes for ECDSA. This expansion affects bandwidth, storage, and processing capacity across infrastructure.
Hardware security modules designed for RSA and ECC may lack capacity for post-quantum workloads. Network appliances might struggle with increased computational overhead. Embedded devices with limited resources may require hardware replacement rather than software updates.
Applications with tight cryptographic coupling need code changes. Legacy systems may lack required libraries for approved algorithms. Protocol changes ripple through entire technology stacks, requiring coordination across multiple teams and vendors.
Approved algorithms vary by entity and asset category. Category 1 entities using Category A assets must employ national cryptography plus post-quantum algorithms with 256-bit minimum security. Category 1 entities using Category B assets can use SHA-2/SHA-3, AES, ChaCha20, ML-DSA, SLH-DSA, and ML-KEM with appropriate modes and security levels. Category 2 entities can use ML-DSA, SLH-DSA, ML-KEM, ECDSA, EdDSA, RSA (3072-bit minimum), ECDH, and approved key establishment methods.
The Six-Phase Migration Process
The regulation defines a structured Migration Process comprising six mandatory phases:
Phase 0: Call for Migration
Organizations receive official communication about the regulation and necessary documentation. Entities must review requirements thoroughly, acknowledge receipt of notification, designate a compliance lead, establish contact with regulatory authorities, and attend introductory meetings and awareness sessions.
Phase 1: Migration Analysis
Organizations conduct comprehensive reviews of regulatory requirements, create inventories of cryptographic assets, and perform migration analysis focusing on identifying gaps, assessing migration impact and associated risks, and finding mitigation strategies.
Phase 2: Migration Plan Proposal
Organizations develop comprehensive migration plans informed by Phase 1 analysis and submit plans for review and approval. Migration plans must be provided within 180 days from initial regulatory communication and include lists of critical assets with current encryption methods.
Phase 3: Migration Plan Review
Regulatory authorities review proposed migration plans and provide detailed feedback and recommendations. Organizations incorporate feedback as instructed, after which authorities approve the migration plan.
Phase 4: Migration Execution
Organizations execute actions detailed in approved migration plans with adherence to approved timelines. This execution leads to actual updating of cryptographic assets to achieve regulatory compliance. Migration must be fully completed within the period defined in the approved plan.
Phase 5: Migration Audit
Organizations conduct internal audits followed by external audits organized by regulatory authorities. If gaps are identified, organizations take remedial actions as instructed. Both audits ensure quality and compliance status of migration execution. Entities receive Migration Compliance Certificates after successful completion, indicating the end of the migration process.
Quantum computing is advancing fast enough to challenge the encryption that secures critical systems across the UAE. The nation has taken a decisive step ahead of that risk with Executive Regulation No. 71 of 2024, issued by the UAE Cybersecurity Council. This regulation mandates a structured cryptographic migration program for government and vital sector entities, shifting away from vulnerable classical algorithms toward quantum-resistant controls.
A Post-Quantum Cryptography Readiness Assessment allows organizations to measure their exposure, identify weak cryptographic assets, and prepare for the UAE’s transition cycle without disrupting essential services. The assessment becomes the foundation for long-term confidentiality, system integrity, and compliance with national cryptographic requirements.
Quantum computing is now a pressing issue for national security and the economy, not just a future concern. The UAE has demonstrated proactive leadership worldwide by approving the National Encryption Policy and issuing its mandatory Executive Regulation to protect the country’s digital infrastructure in the quantum age.
The Harvest Now, Decrypt Later Problem
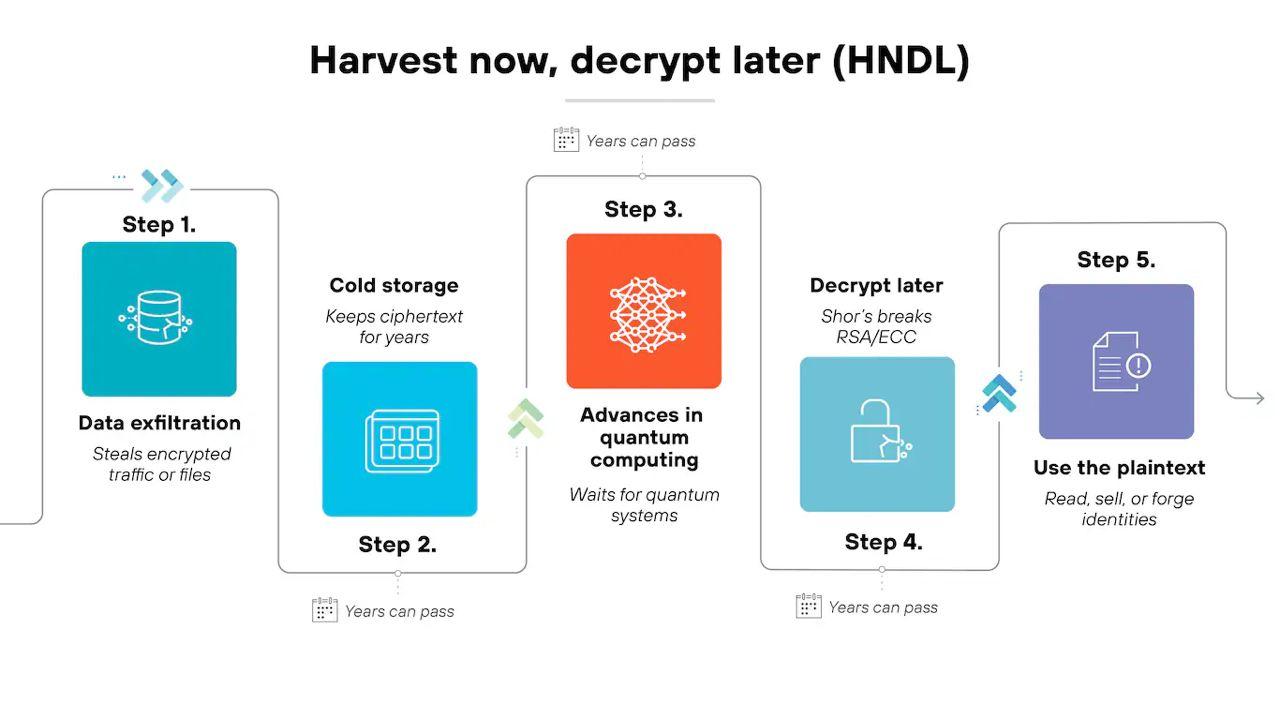
Sophisticated adversaries capture encrypted communications and databases today, storing them until quantum computers can break the protection. Your RSA or ECC-encrypted data from today could be exposed years from now when it still holds value.
Financial transactions, patient records, classified information, and intellectual property all face this threat. Any data requiring confidentiality beyond five to ten years needs quantum-resistant protection immediately.
Understanding Cryptographic Assets
Cryptographic assets are tools or services that provide cryptographic security for data and communications critical to organizational operations. These include software such as code, libraries, applications, and implementations of cryptographic algorithms or protocols. They also encompass data like certificates and cryptographic keys, as well as hardware tokens, HSMs (Hardware Security Modules), smart cards, trusted execution environments (TEEs), and physical pseudorandom generators.
The regulation classifies cryptographic assets into two critical categories:
Category A – Highly Sensitive Assets:
- Encryption Devices and Virtual Private Networks (VPNs)
- Radio Communication Solutions
- Key Management Systems
- Secure Communication Solutions (Email Security Systems, Secure Messaging Application Systems, Audio/Video Applications, Web Conferencing)
Category B – Support Infrastructure:
- Cloud Encryption Solutions
- File and Data Sharing Solutions
- Network Devices (Firewalls, Routers)
- Smart Card Readers
- PLC and SCADA Systems
All these assets are subject to mandatory migration and compliance verification under the regulatory framework.
Why Organizations Need a Structured PQC Readiness Assessment
Quantum impact is uneven across industries. Financial services, telecom operators, governments, energy providers, healthcare institutions, and global enterprises hold data that must remain confidential for decades. A breach today carries a long tail because attackers can store encrypted material until it becomes solvable.
NIST has already standardized its first set of quantum-resistant algorithms. Major vendors are shipping hybrid modes that combine classical and PQC primitives. International bodies such as ETSI, IETF, and ISO are defining transition rules. The regulatory shift has already begun.
A readiness assessment gives teams the groundwork required to move without causing operational disruption. It answers three core questions:
Which systems depend on cryptography today?
Which components break the moment PQC becomes a requirement?
What must be replaced, upgraded, or redesigned to maintain confidentiality and authenticity?
The organizations that move early reduce both the migration effort and the cost of downtime. Many crypto assets live much longer than expected, and replacing them under pressure is significantly harder. Long-lived certificates, archived backups, and stored sensitive records all fall into this category.
Minimum Cryptographic Requirements
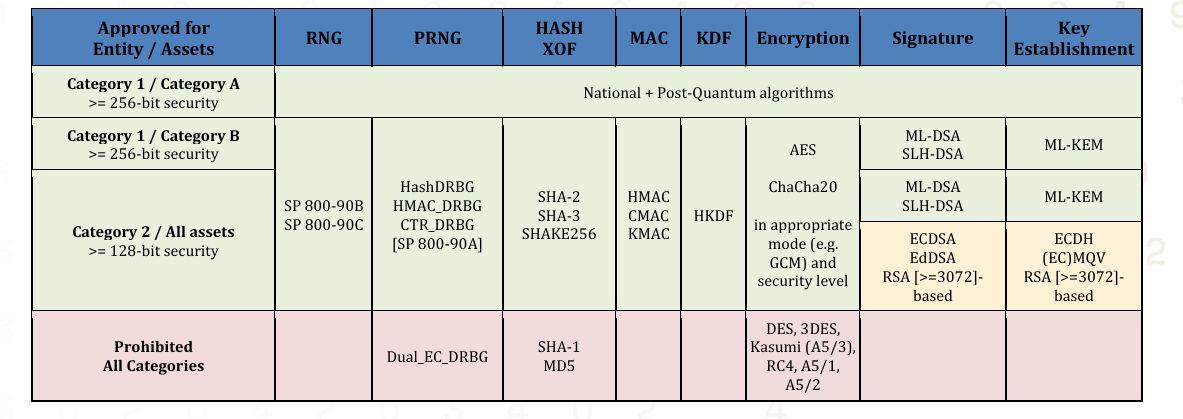
The regulation establishes specific minimum cryptographic requirements for each entity category.
Category 1 Entities Must:
- Achieve cryptographic agility
- Use at least 256-bit security/PQC Category 5 security strength
- Use approved Category A assets (VPN, ESS, SMAS)
- Employ national cryptography for Category A assets minimum
- Implement post-quantum cryptography
- Use approved hardware-protected cryptography when applicable
- Utilize cryptographic certificates from approved certificate authorities
Category 2 Entities Must:
- Use at least 128-bit security strength
- Employ standard cryptography
Category 2 entities are recommended to use post-quantum cryptography with security strength meeting established standards.
The regulation explicitly prohibits certain algorithms. Unless explicitly authorized, any algorithms not mentioned in the regulations are considered unapproved and cannot be used. Banned algorithms include Dual_EC_DRBG, SHA-1, MD5, DES, 3DES, Kasumi (A5/3), RC4, A5/1, and A5/2.
Technical Migration Realities
Post-quantum algorithms require larger keys than current standards. ML-KEM public keys need 1,184 bytes versus 256 bytes for RSA-2048. ML-DSA signatures use around 3,309 bytes compared to 256 bytes for ECDSA. This expansion affects bandwidth, storage, and processing capacity across infrastructure.
Hardware security modules designed for RSA and ECC may lack capacity for post-quantum workloads. Network appliances might struggle with increased computational overhead. Embedded devices with limited resources may require hardware replacement rather than software updates.
Applications with tight cryptographic coupling need code changes. Legacy systems may lack required libraries for approved algorithms. Protocol changes ripple through entire technology stacks, requiring coordination across multiple teams and vendors.
Approved algorithms vary by entity and asset category. Category 1 entities using Category A assets must employ national cryptography plus post-quantum algorithms with 256-bit minimum security. Category 1 entities using Category B assets can use SHA-2/SHA-3, AES, ChaCha20, ML-DSA, SLH-DSA, and ML-KEM with appropriate modes and security levels. Category 2 entities can use ML-DSA, SLH-DSA, ML-KEM, ECDSA, EdDSA, RSA (3072-bit minimum), ECDH, and approved key establishment methods.
The Six-Phase Migration Process
The regulation defines a structured Migration Process comprising six mandatory phases:
Phase 0: Call for Migration
Organizations receive official communication about the regulation and necessary documentation. Entities must review requirements thoroughly, acknowledge receipt of notification, designate a compliance lead, establish contact with regulatory authorities, and attend introductory meetings and awareness sessions.
Phase 1: Migration Analysis
Organizations conduct comprehensive reviews of regulatory requirements, create inventories of cryptographic assets, and perform migration analysis focusing on identifying gaps, assessing migration impact and associated risks, and finding mitigation strategies.
Phase 2: Migration Plan Proposal
Organizations develop comprehensive migration plans informed by Phase 1 analysis and submit plans for review and approval. Migration plans must be provided within 180 days from initial regulatory communication and include lists of critical assets with current encryption methods.
Phase 3: Migration Plan Review
Regulatory authorities review proposed migration plans and provide detailed feedback and recommendations. Organizations incorporate feedback as instructed, after which authorities approve the migration plan.
Phase 4: Migration Execution
Organizations execute actions detailed in approved migration plans with adherence to approved timelines. This execution leads to actual updating of cryptographic assets to achieve regulatory compliance. Migration must be fully completed within the period defined in the approved plan.
Phase 5: Migration Audit
Organizations conduct internal audits followed by external audits organized by regulatory authorities. If gaps are identified, organizations take remedial actions as instructed. Both audits ensure quality and compliance status of migration execution. Entities receive Migration Compliance Certificates after successful completion, indicating the end of the migration process.
Technical Realities
Post-quantum algorithms require larger keys than current standards. ML-KEM public keys need 1,184 bytes versus 256 bytes for RSA-2048. ML-DSA signatures use around 3,309 bytes compared to 256 bytes for ECDSA. This expansion affects bandwidth, storage, and processing capacity across infrastructure.
Hardware security modules designed for RSA and ECC may lack capacity for post-quantum workloads. Network appliances might struggle with increased computational overhead. Embedded devices with limited resources may require hardware replacement rather than software updates.
Applications with tight cryptographic coupling need code changes. Legacy systems may lack required libraries for approved algorithms. Protocol changes ripple through entire technology stacks, requiring coordination across multiple teams and vendors.
Approved algorithms vary by entity and asset category. Category 1 entities using Category A assets must employ national cryptography plus post-quantum algorithms with 256-bit minimum security. Category 1 entities using Category B assets can use SHA-2/SHA-3, AES, ChaCha20, ML-DSA, SLH-DSA, and ML-KEM with appropriate modes and security levels. Category 2 entities can use ML-DSA, SLH-DSA, ML-KEM, ECDSA, EdDSA, RSA (3072-bit minimum), ECDH, and approved key establishment methods.
Technical Realities
Post-quantum algorithms require larger keys than current standards. ML-KEM public keys need 1,184 bytes versus 256 bytes for RSA-2048. ML-DSA signatures use around 3,309 bytes compared to 256 bytes for ECDSA. This expansion affects bandwidth, storage, and processing capacity across infrastructure.
Hardware security modules designed for RSA and ECC may lack capacity for post-quantum workloads. Network appliances might struggle with increased computational overhead. Embedded devices with limited resources may require hardware replacement rather than software updates.
Applications with tight cryptographic coupling need code changes. Legacy systems may lack required libraries for approved algorithms. Protocol changes ripple through entire technology stacks, requiring coordination across multiple teams and vendors.
Approved algorithms vary by entity and asset category. Category 1 entities using Category A assets must employ national cryptography plus post-quantum algorithms with 256-bit minimum security. Category 1 entities using Category B assets can use SHA-2/SHA-3, AES, ChaCha20, ML-DSA, SLH-DSA, and ML-KEM with appropriate modes and security levels. Category 2 entities can use ML-DSA, SLH-DSA, ML-KEM, ECDSA, EdDSA, RSA (3072-bit minimum), ECDH, and approved key establishment methods.
Building Flexibility
Successful quantum readiness requires crypto-agility—the ability to change algorithms quickly as standards evolve or threats emerge.
Applications should reference algorithms through configuration, not hardcode them. Certificate management needs automation for issuing, deploying, renewing, and revoking at scale. Key management must support hybrid approaches where classical and post-quantum algorithms coexist.
Hybrid cryptography offers a practical path. Systems employ traditional RSA or ECC alongside post-quantum algorithms, maintaining compatibility while adding quantum resistance. This protects against both attack types during transition.
Shorten credential lifespans. Long-lived certificates increase exposure for harvest-now-decrypt-later attacks. Just-in-time access with ephemeral credentials limits intercepted material value.
Regulatory Requirements
The U.S. Quantum Computing Cybersecurity Preparedness Act requires federal agencies to inventory cryptographic systems and transition to quantum-resistant algorithms. This sets precedent for private sector requirements.
FDA cybersecurity guidance demands crypto-agility throughout medical device lifecycles. The agency can refuse approvals for devices using deprecated algorithms or lacking migration paths.
Financial sector regulators push quantum preparedness through industry organizations. FS-ISAC published guidance stating moves to crypto-agility must begin immediately. Europol’s Quantum Safe Financial Forum issued urgent calls for coordinated transitions.
Quantum readiness is now a compliance obligation. Organizations with proactive PQC assessment and migration planning gain favor with regulators, auditors, customers, and partners.
Phased Migration Approach
Successful transitions follow structured stages.
Discovery Phase: Inventory cryptographic assets, classify risks, analyze gaps against quantum-safe standards, and engage vendors about roadmaps.
Pilot Phase: Test post-quantum algorithms in non-production systems. Measure performance impacts, identify integration challenges, and validate procedures.
Implementation Phase: Roll out quantum-safe cryptography systematically. High-risk assets transition first, followed by medium and lower-priority systems.
Throughout each phase, monitor compliance with evolving standards, track vendor progress, and adjust timelines as needed.
How DTS Solution Supports Your PQC Readiness
Cryptographic Discovery
We scan your entire IT environment—on-premises, cloud, and hybrid systems—to identify all cryptographic assets. Our comprehensive discovery process finds certificates, keys, algorithms, libraries, and protocols across endpoints, applications, APIs, network devices, databases, and embedded systems.
We identify systems utilizing cryptography, from authentication servers and HSMs to load balancers, VPNs, and more. You receive a detailed inventory with algorithm types, key sizes, expiration dates, and certificate chains that serves as your baseline for risk assessment.
Risk Assessment and Gap Analysis
DTS Solution evaluates your cryptographic infrastructure against NIST-approved standards and NSA’s CNSA 2.0 requirements. We analyze which elements face quantum threats, particularly those relying on RSA, ECC, and other vulnerable algorithms.
We review how your PKI and HSMs are configured and whether they support post-quantum algorithm integration. Our team analyzes applications for hardcoded cryptographic dependencies and identifies those requiring refactoring.
You receive a detailed report with vulnerable asset inventory, risk severity ratings, and migration prioritization.
Custom Migration Strategy
We develop a phased migration roadmap aligned with your business requirements, risk profile, and regulatory obligations. Our strategy reflects your risk appetite and industry best practices.
DTS Solution designs systems and workflows to support easy algorithm switching as standards evolve. We update security policies, key management procedures, and compliance rules to align with NIST and NSA recommendations.
Your roadmap includes short-, medium-, and long-term goals broken into manageable phases: pilot programs, hybrid deployment, and full implementation.
Vendor Evaluation and Testing
We help you identify and test the right tools, technologies, and partners. Our team defines technical and business requirements for RFIs and RFPs, including algorithm support, integration compatibility, and performance.
DTS Solution identifies top vendors offering PQC-capable PKI, key management, and cryptographic solutions. We run proof-of-concept tests in isolated environments to evaluate performance, integration ease, and fit for your use cases.
You receive a vendor comparison matrix and recommendation report based on real-world findings.
Implementation Support
We validate everything through controlled pilots before full deployment. Testing occurs in sandbox or non-production environments for one or two applications. We validate interoperability with existing systems, third-party dependencies, and legacy components.
After successful testing, DTS Solution supports smooth, scalable rollout. We replace legacy algorithms step by step, minimizing disruption while ensuring systems remain secure and compliant.
Our team provides hands-on training and detailed technical documentation for ongoing maintenance. We set up monitoring and lifecycle management to track cryptographic health and support future upgrades.
Conclusion
Organizations waiting for quantum computers to break encryption will find themselves in crisis. The UK’s National Cyber Security Centre marked 2028 as its first major PQC milestone—less than three years away.
Quantum readiness requires multi-year planning and execution. Discovery, assessment, piloting, vendor coordination, and phased rollout take time.
Contact DTS Solution to schedule a comprehensive PQC readiness assessment. We’ll examine your cryptographic infrastructure, identify vulnerabilities, and develop a customized roadmap that protects your organization as quantum computing advances.
The quantum threat is real. Start your assessment with DTS Solution and build the cryptographic resilience your business needs.
Building Flexibility
Successful quantum readiness requires crypto-agility—the ability to change algorithms quickly as standards evolve or threats emerge.
Applications should reference algorithms through configuration, not hardcode them. Certificate management needs automation for issuing, deploying, renewing, and revoking at scale. Key management must support hybrid approaches where classical and post-quantum algorithms coexist.
Hybrid cryptography offers a practical path. Systems employ traditional RSA or ECC alongside post-quantum algorithms, maintaining compatibility while adding quantum resistance. This protects against both attack types during transition.
Shorten credential lifespans. Long-lived certificates increase exposure for harvest-now-decrypt-later attacks. Just-in-time access with ephemeral credentials limits intercepted material value.
Regulatory Requirements
The U.S. Quantum Computing Cybersecurity Preparedness Act requires federal agencies to inventory cryptographic systems and transition to quantum-resistant algorithms. This sets precedent for private sector requirements.
FDA cybersecurity guidance demands crypto-agility throughout medical device lifecycles. The agency can refuse approvals for devices using deprecated algorithms or lacking migration paths.
Financial sector regulators push quantum preparedness through industry organizations. FS-ISAC published guidance stating moves to crypto-agility must begin immediately. Europol’s Quantum Safe Financial Forum issued urgent calls for coordinated transitions.
Quantum readiness is now a compliance obligation. Organizations with proactive PQC assessment and migration planning gain favor with regulators, auditors, customers, and partners.
Phased Migration Approach
Successful transitions follow structured stages.
Discovery Phase: Inventory cryptographic assets, classify risks, analyze gaps against quantum-safe standards, and engage vendors about roadmaps.
Pilot Phase: Test post-quantum algorithms in non-production systems. Measure performance impacts, identify integration challenges, and validate procedures.
Implementation Phase: Roll out quantum-safe cryptography systematically. High-risk assets transition first, followed by medium and lower-priority systems.
Throughout each phase, monitor compliance with evolving standards, track vendor progress, and adjust timelines as needed.
How DTS Solution Supports Your PQC Readiness
Cryptographic Discovery
We scan your entire IT environment—on-premises, cloud, and hybrid systems—to identify all cryptographic assets. Our comprehensive discovery process finds certificates, keys, algorithms, libraries, and protocols across endpoints, applications, APIs, network devices, databases, and embedded systems.
We identify systems utilizing cryptography, from authentication servers and HSMs to load balancers, VPNs, and more. You receive a detailed inventory with algorithm types, key sizes, expiration dates, and certificate chains that serves as your baseline for risk assessment.
Risk Assessment and Gap Analysis
DTS Solution evaluates your cryptographic infrastructure against NIST-approved standards and NSA’s CNSA 2.0 requirements. We analyze which elements face quantum threats, particularly those relying on RSA, ECC, and other vulnerable algorithms.
We review how your PKI and HSMs are configured and whether they support post-quantum algorithm integration. Our team analyzes applications for hardcoded cryptographic dependencies and identifies those requiring refactoring.
You receive a detailed report with vulnerable asset inventory, risk severity ratings, and migration prioritization.
Custom Migration Strategy
We develop a phased migration roadmap aligned with your business requirements, risk profile, and regulatory obligations. Our strategy reflects your risk appetite and industry best practices.
DTS Solution designs systems and workflows to support easy algorithm switching as standards evolve. We update security policies, key management procedures, and compliance rules to align with NIST and NSA recommendations.
Your roadmap includes short-, medium-, and long-term goals broken into manageable phases: pilot programs, hybrid deployment, and full implementation.
Vendor Evaluation and Testing
We help you identify and test the right tools, technologies, and partners. Our team defines technical and business requirements for RFIs and RFPs, including algorithm support, integration compatibility, and performance.
DTS Solution identifies top vendors offering PQC-capable PKI, key management, and cryptographic solutions. We run proof-of-concept tests in isolated environments to evaluate performance, integration ease, and fit for your use cases.
You receive a vendor comparison matrix and recommendation report based on real-world findings.
Implementation Support
We validate everything through controlled pilots before full deployment. Testing occurs in sandbox or non-production environments for one or two applications. We validate interoperability with existing systems, third-party dependencies, and legacy components.
After successful testing, DTS Solution supports smooth, scalable rollout. We replace legacy algorithms step by step, minimizing disruption while ensuring systems remain secure and compliant.
Our team provides hands-on training and detailed technical documentation for ongoing maintenance. We set up monitoring and lifecycle management to track cryptographic health and support future upgrades.
Conclusion
Organizations waiting for quantum computers to break encryption will find themselves in crisis. The UK’s National Cyber Security Centre marked 2028 as its first major PQC milestone—less than three years away.
Quantum readiness requires multi-year planning and execution. Discovery, assessment, piloting, vendor coordination, and phased rollout take time.
Contact DTS Solution to schedule a comprehensive PQC readiness assessment. We’ll examine your cryptographic infrastructure, identify vulnerabilities, and develop a customized roadmap that protects your organization as quantum computing advances.
The quantum threat is real. Start your assessment with DTS Solution and build the cryptographic resilience your business needs.
See also:




